Some notes from updating 17 of my own nodes to v1.1.2 over 4 platforms (DO, Linode, GCP, AWS):
-
If your node was launched via NKN official 1-click on DO, there is nothing you need to do. It will automatically update and just work.
-
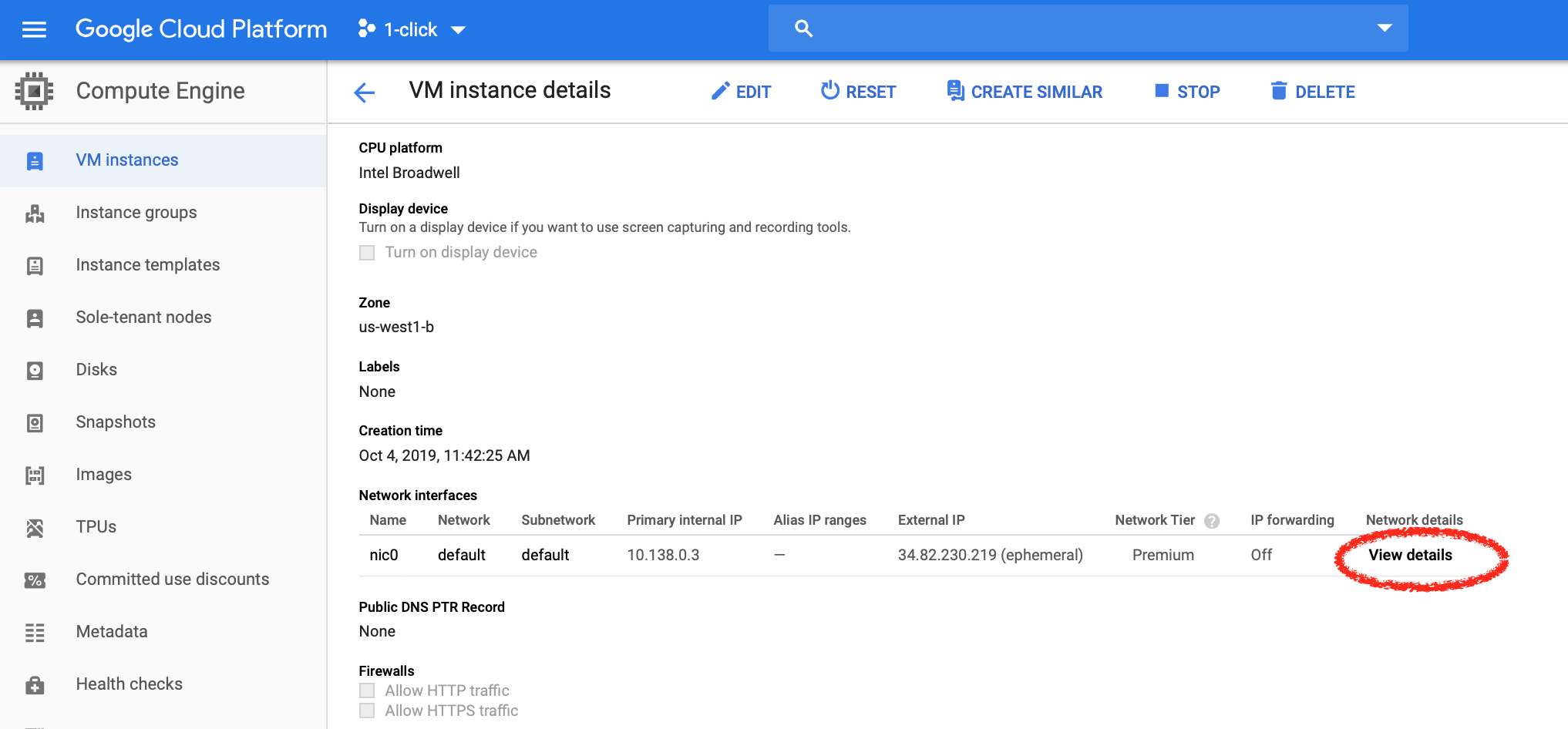
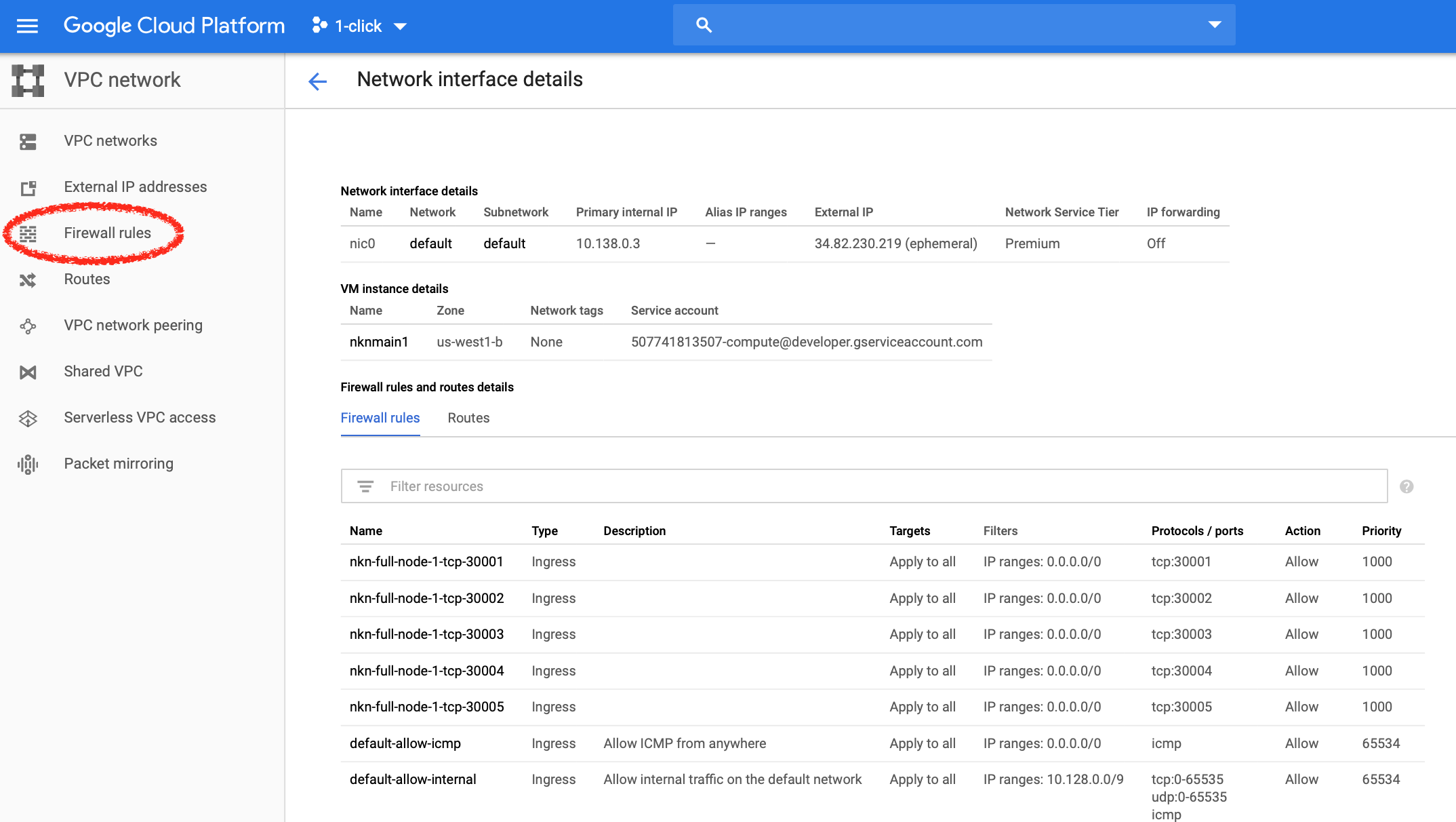
If your node was launched via NKN Official 1-click on GCP and AWS, the NKN software itself will be updated automatically.
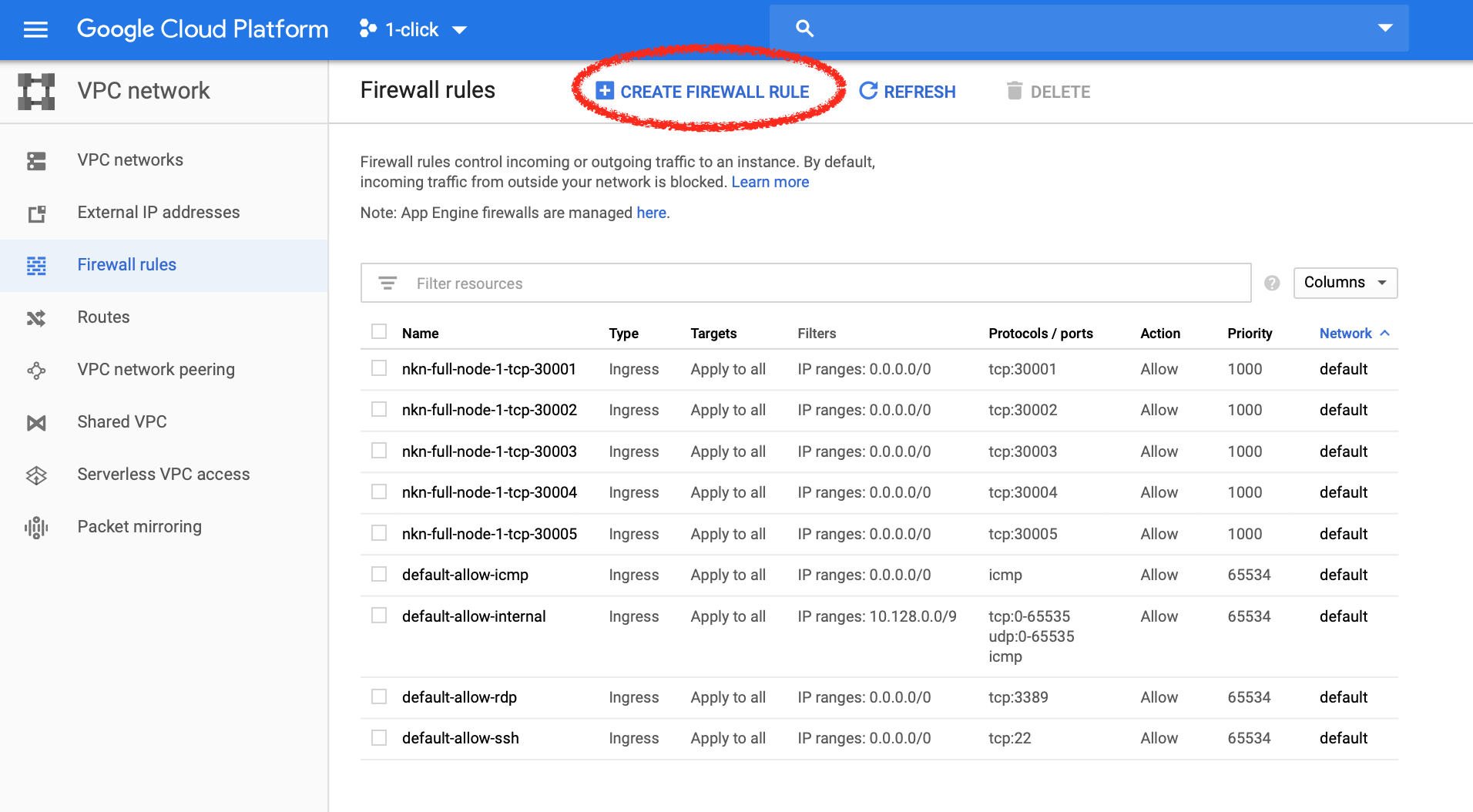
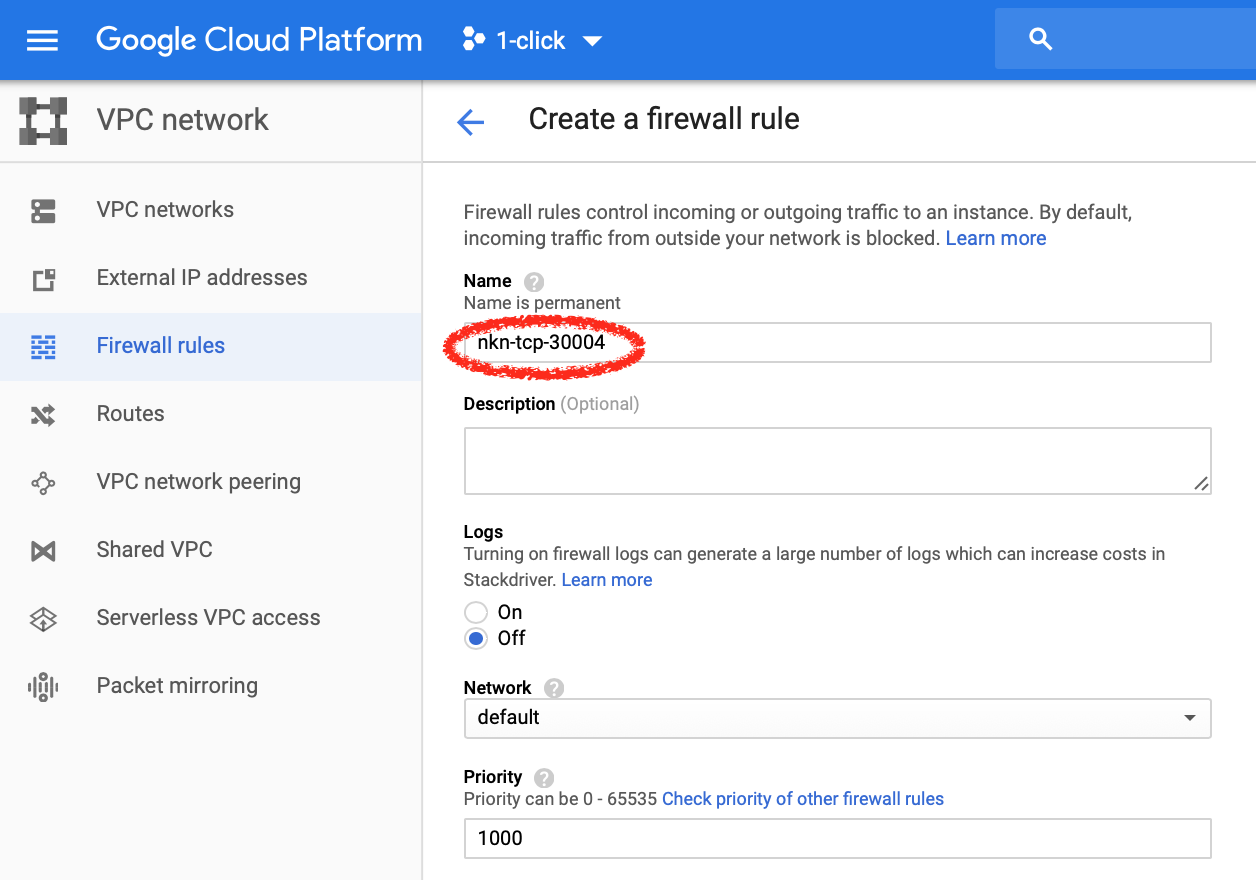
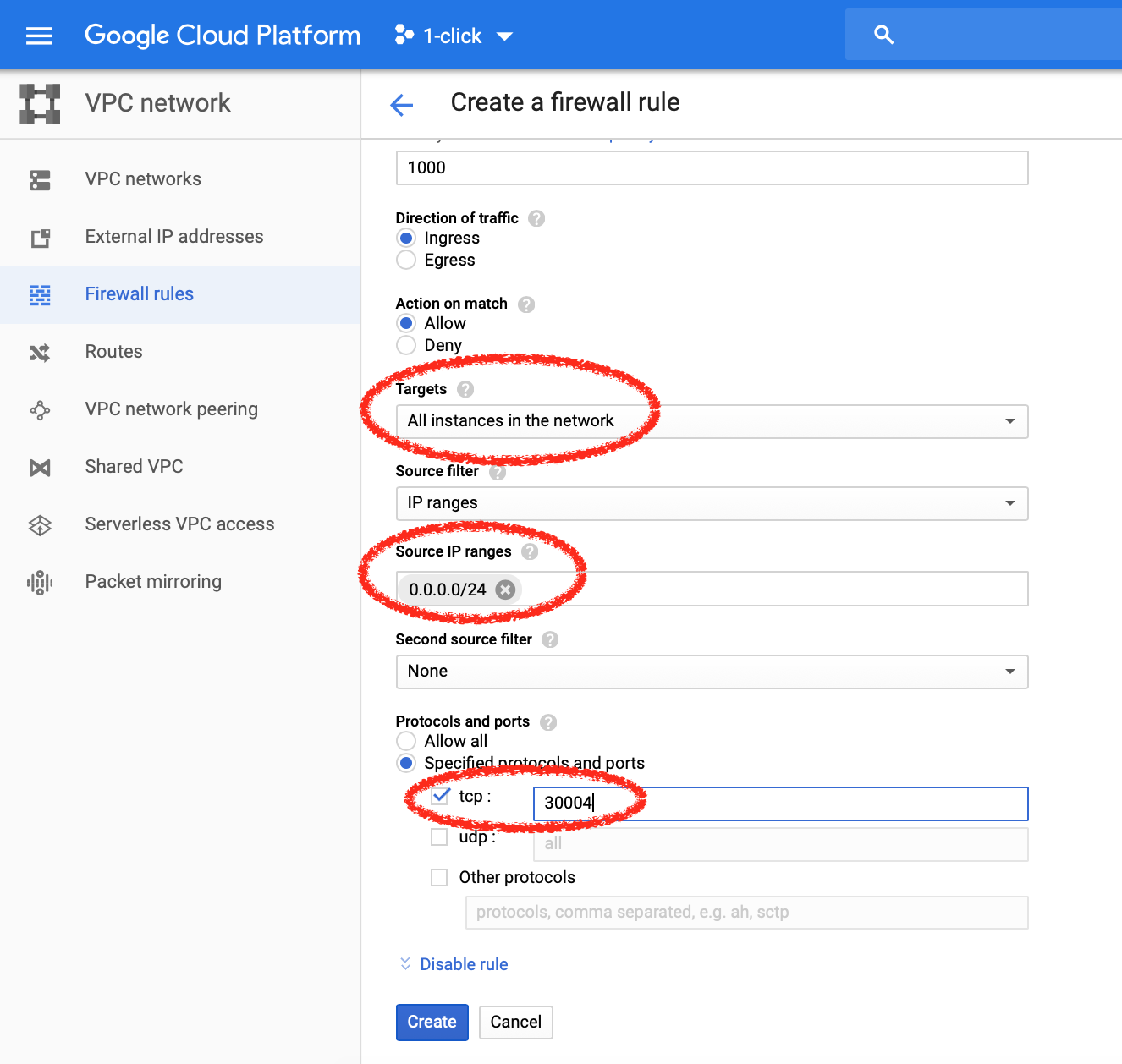
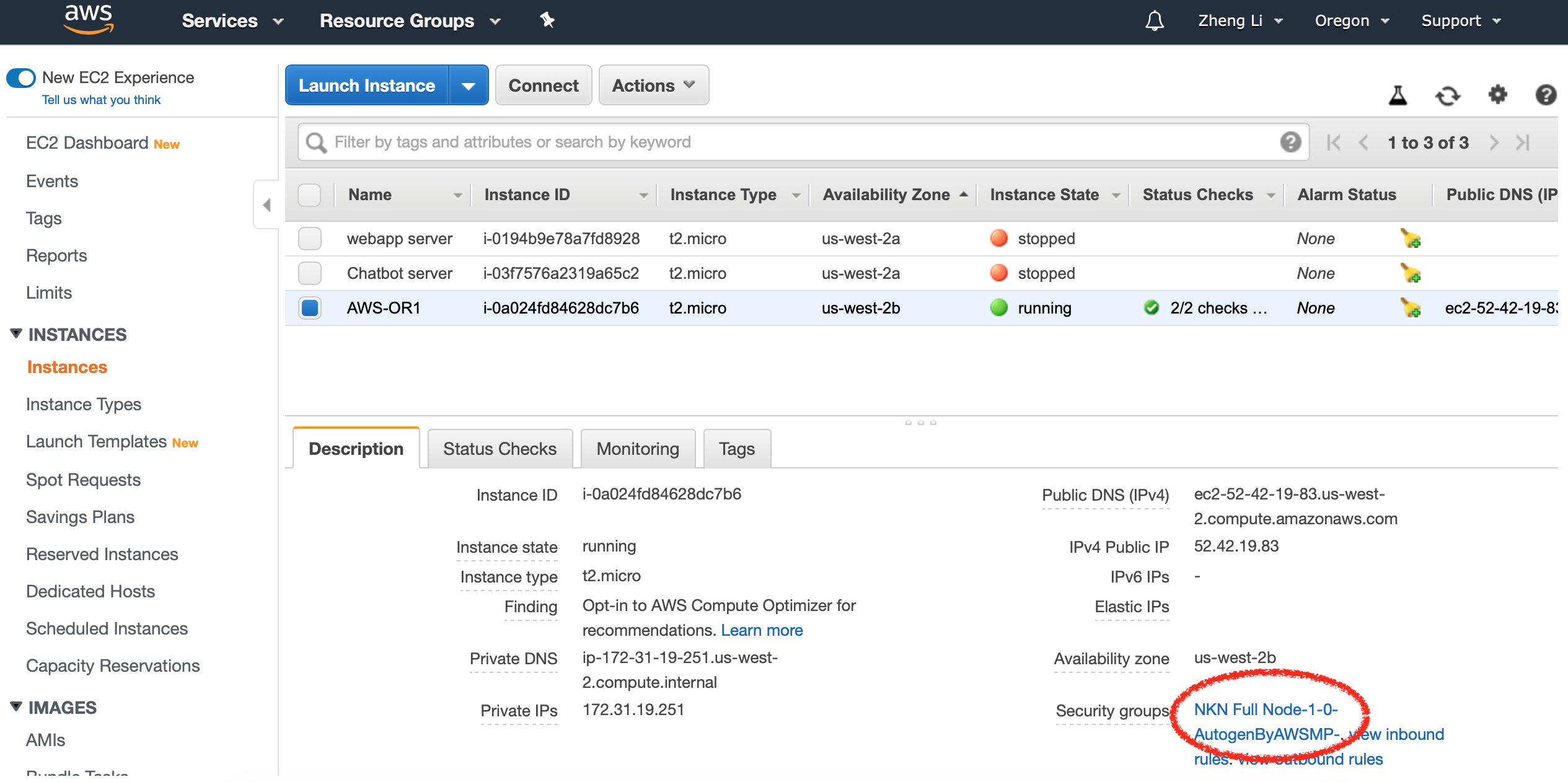
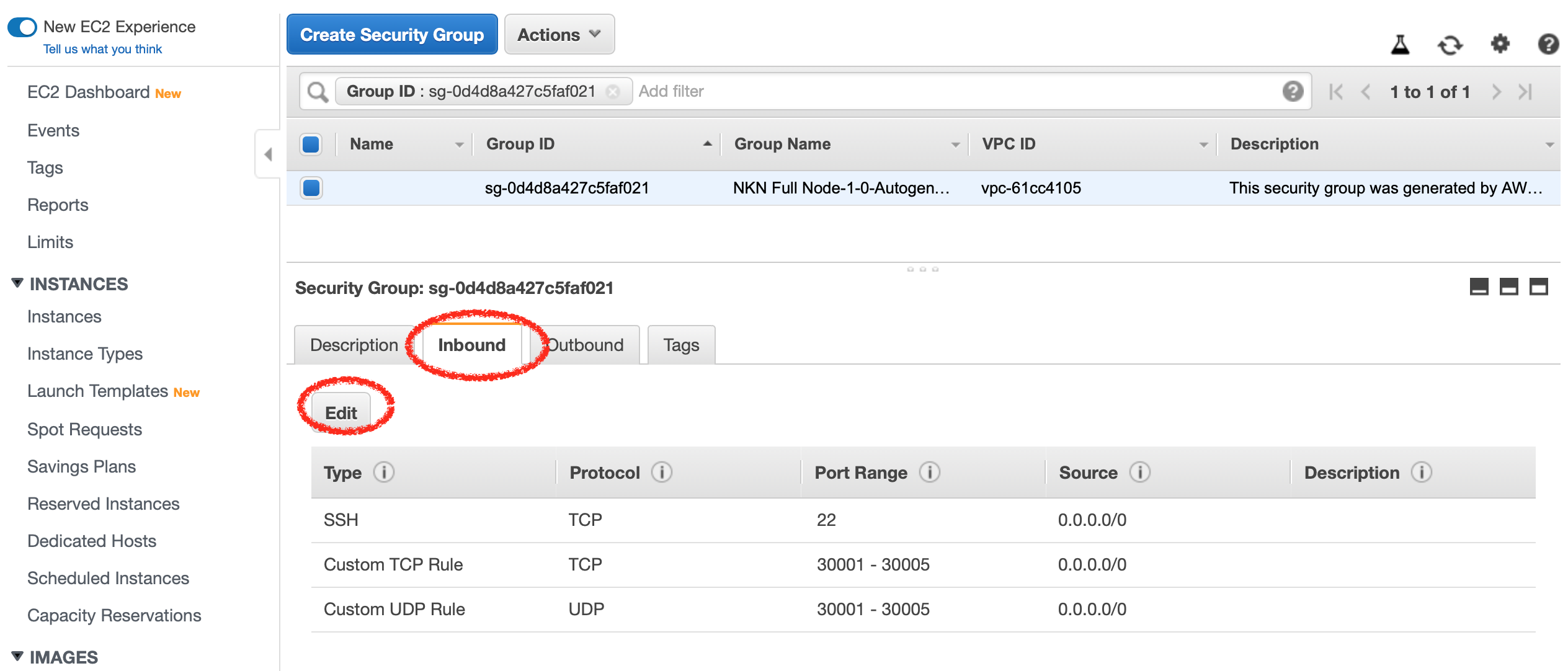
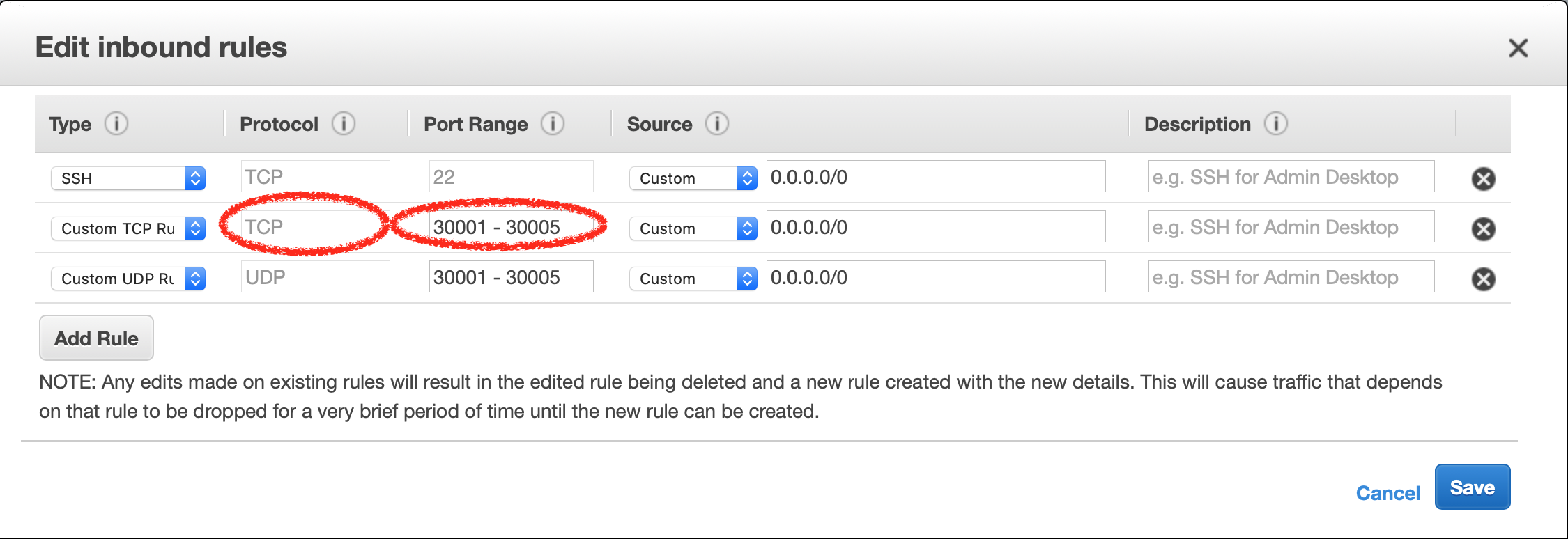
BUT you need to add firewall rules in admin console to allow opening port 30004 and 30005. In AWS, it can be configured in Security Group that is associated with your VM. In GCP, it can be configured in Firewall Inbound Rules in Network configuration.
We are in the process of updating the 1-clicks, so once those are approved any new node launched via 1-click should already include the latest firewall rules.
-
If your node was launched via NKNx “Fast Deploy”, you need to log into your VM, and run these two commands as root user. You only need to do this ONCE.
ufw allow 30004
ufw allow 30005In addition, if your “Fast Deploy” nodes were on GCP or AWS, you need to do the same firewall setting in admin console as above point 2.
-
I forgot if my node was launched via NKN official 1-click or NKNx Fast Deploy, how can I find out?
If you log into your VM, and run command “
ls /home”. If you find folder nkn then it is 1-click; if you find nknx then it is Fast Deploy. -
If you do need to log into your VM or droplet, it is advisable to use this opportunity to update the operations system so all security patches are applied. You can run the following as root user:
apt-get update
apt-get upgrade -
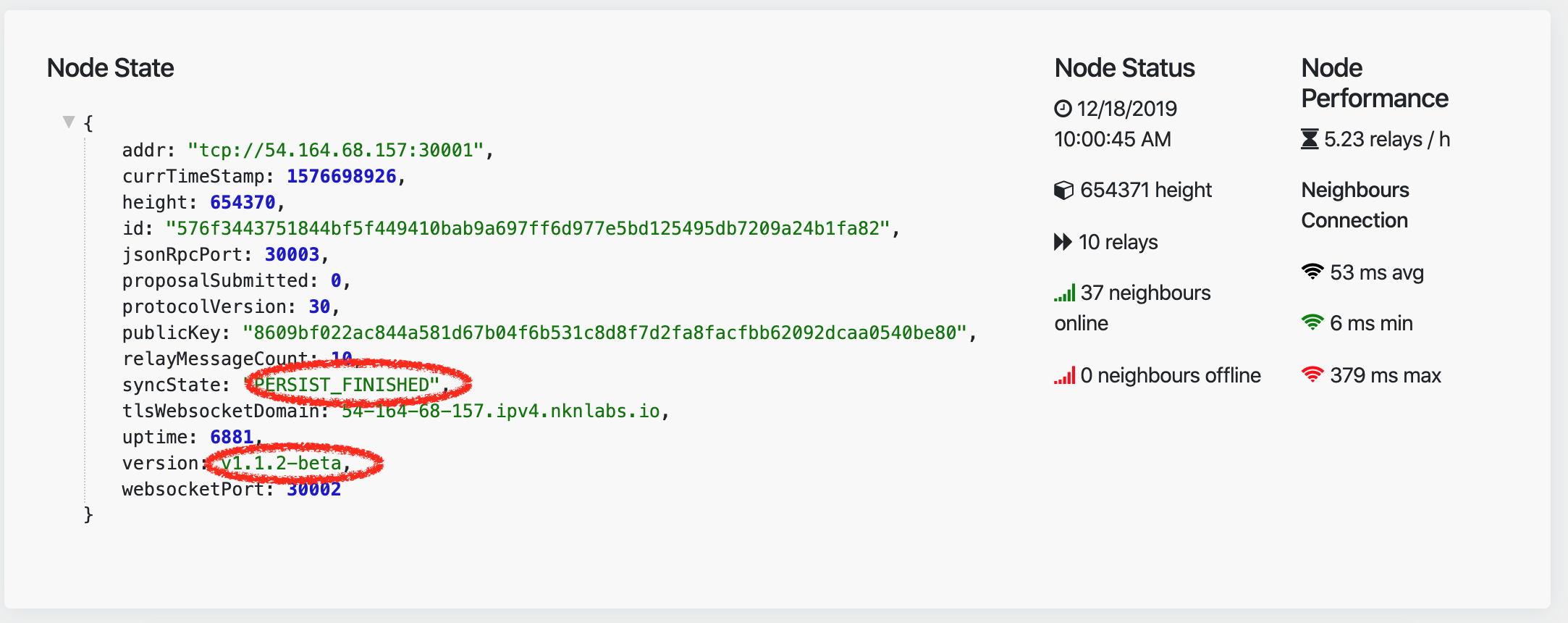
To check if your node is updated properly, you can use
- http://nstatus.org to check if your node is updated to the right software version (1.1.2) and if it is mining properly.
-
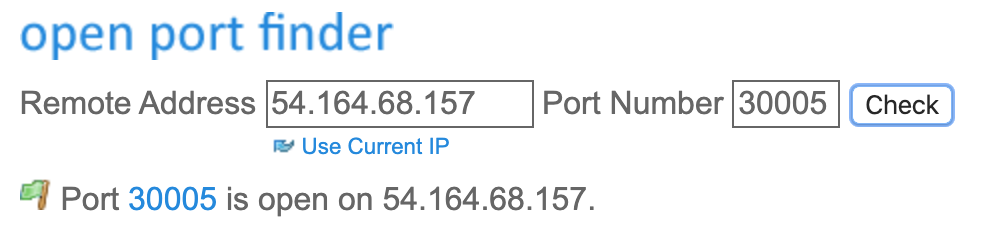
https://www.yougetsignal.com/tools/open-ports/ to check if your node’s ports are properly open (30001 to 30005)